Data Compression
Explore data compression techniques that reduce file size for efficient storage and transmission. Compare lossless compression (original data perfectly recoverable, used for text and executables) with lossy compression (some data discarded, used for images/audio/video). Visualize run-length encoding (RLE) that replaces repeated sequences with count-value pairs, and understand Huffman coding, LZW, and how compression ratios balance file size with quality.
Pixel & Image Representation
Understand how digital images are represented as grids of pixels, each storing color information. Explore the RGB color model where each pixel combines Red, Green, and Blue values (0-255) to create millions of colors. Learn how resolution (pixel dimensions) and bit depth affect image quality and file size, and understand the relationship between pixels, screen resolution, and how computers store and display visual information.
Binary Number System
Explore the binary (base-2) number system used by computers to represent all data. Convert between binary, decimal (base-10), and hexadecimal (base-16) representations. Understand place values as powers of 2, practice binary arithmetic, and learn why computers use binary (two states: 0 and 1 corresponding to off/on electrical signals). Discover how binary represents numbers, text (ASCII/Unicode), images, and all digital information.

Internet Protocols & Routing
Explore how the Internet works through protocols and routing. Understand the TCP/IP protocol suite: IP addresses for device identification, TCP for reliable data transmission with error checking, and UDP for faster connectionless communication. Visualize packet routing through networks, DNS (Domain Name System) translating domain names to IP addresses, and how routers use routing tables to forward packets along optimal paths across the global Internet infrastructure.
Encryption & Ciphers
Explore encryption techniques that protect data confidentiality by transforming plaintext into ciphertext. Practice classic ciphers like Caesar cipher (shift each letter by a fixed amount) and substitution ciphers. Understand symmetric encryption (same key for encryption and decryption) versus asymmetric encryption (public/private key pairs). Learn about modern encryption standards like AES, RSA, and the importance of cryptography in securing digital communications and online transactions.
RGB Color Mixer & Hex Converter
Interactive RGB color mixing with real-time decimal, hexadecimal, and 24-bit binary conversion. Demonstrates additive color model, 8-bit channel depth (256 levels per channel), and the 16.7M color gamut of modern displays.
Boolean Logic Gate Simulator
Interactive Boolean logic gate simulator with 6 gate types (AND, OR, NOT, NAND, XOR, NOR). Features toggleable binary inputs, live truth tables with highlighted active row, and animated circuit diagrams showing signal propagation.
TCP/IP Packet Routing Simulator
Interactive TCP/IP packet routing through a mesh network. Message splitting into numbered packets, multi-path independent routing, router failure fault tolerance, and reassembly at destination demonstrates the core architecture principles of the Internet.
DNS Resolution Visualizer
Step-by-step DNS resolution animation showing the hierarchical lookup cascade from browser cache through recursive resolver, root server (13 clusters), TLD server (.com/.org), to authoritative nameserver, with caching and TTL concepts.
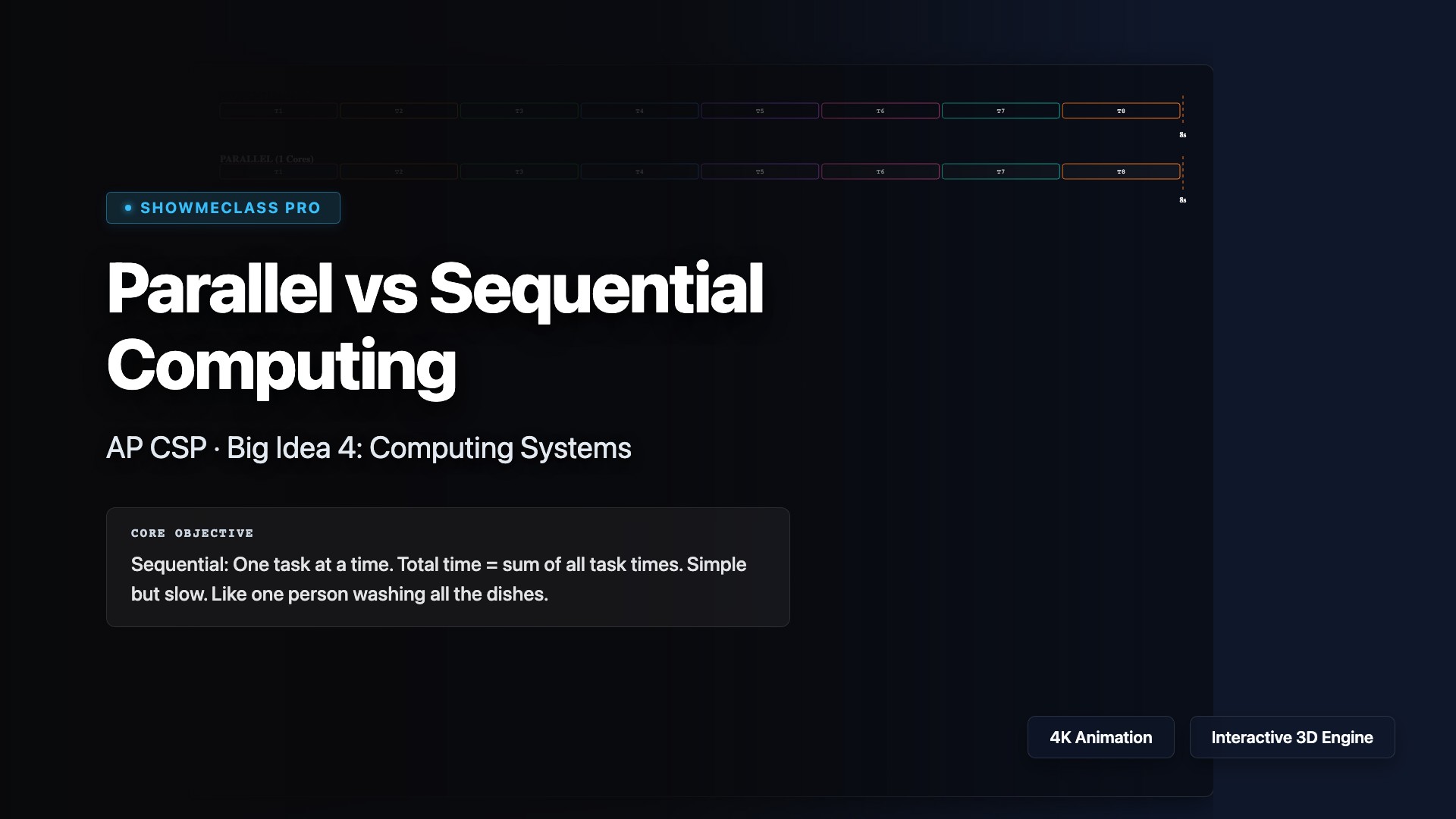
Parallel vs Sequential Computing
Side-by-side visual comparison of sequential vs parallel task scheduling. Adjustable processor cores, task count, and sequential bottleneck percentage demonstrates Amdahl's Law speedup limits, efficiency degradation, and the diminishing returns of adding processors.